Overview
This investigation demonstrates detection of brute-force login activity using Windows Security logs and Wazuh SIEM.
Multiple failed authentication attempts were generated within a short time window. These events were ingested into Wazuh and correlated into a higher severity alert, indicating potential credential access activity.
The lab simulates a real-world SOC scenario where repeated login failures transition from raw logs into actionable security alerts.
Tools Used
- Windows 11
- Windows Security Logs (Event ID 4625)
- Wazuh SIEM
- PowerShell (attack simulation)
Detection
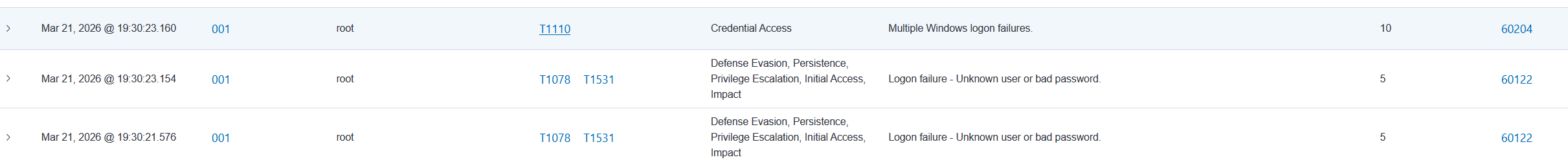
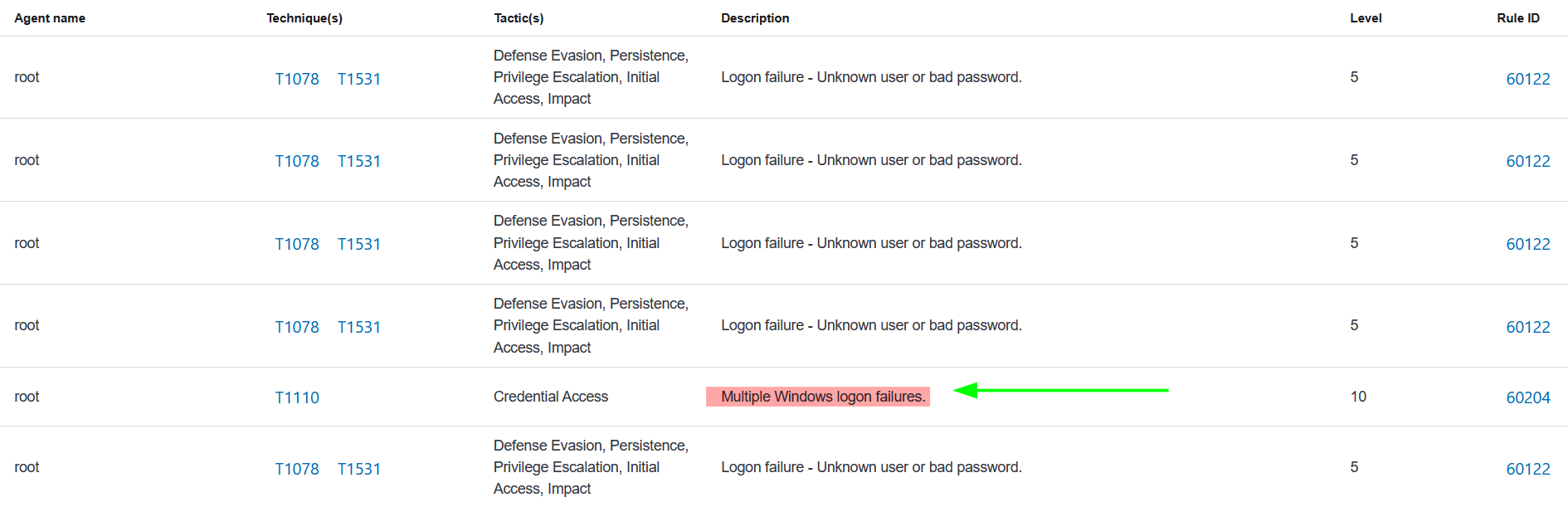
Wazuh generated the following correlated alert:
Attack Simulation
Brute-force activity was simulated using repeated login attempts with invalid credentials.
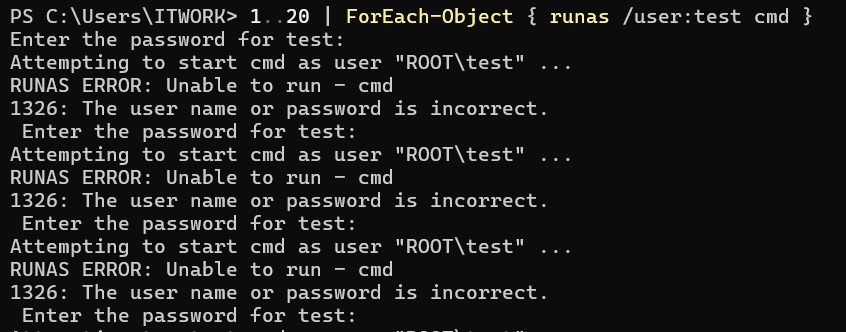
Example command:
1..20 | ForEach-Object { runas /user:test cmd }Windows Event Analysis
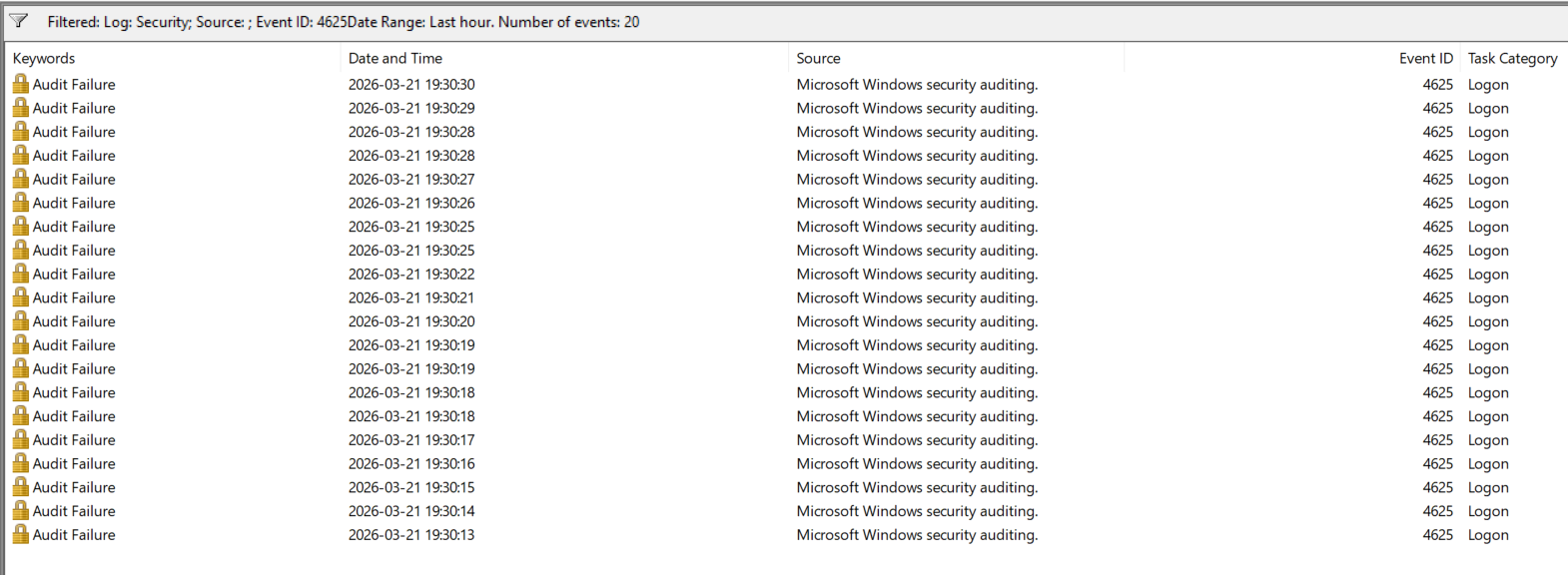
Windows Security logs recorded multiple failed login attempts (Event ID 4625).
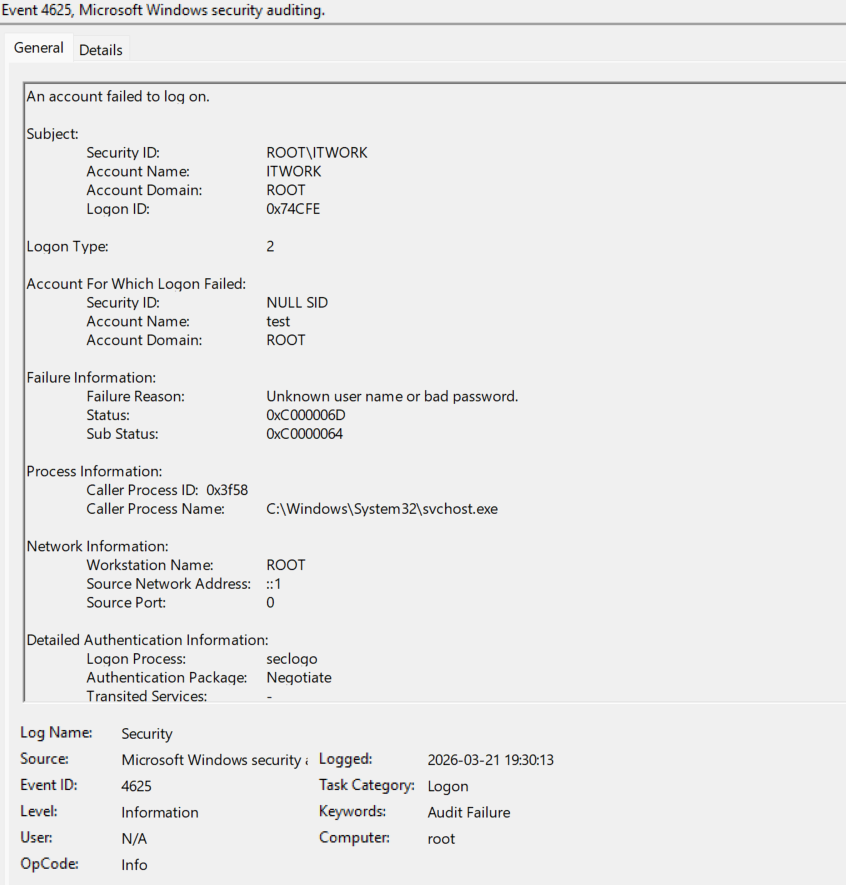
These events contain:
- Target username
- Failure reason
- Logon type
- Source system information
Wazuh Alert Analysis
Wazuh ingested and analyzed the events, generating multiple alerts for failed authentication attempts.
Repeated events were correlated into a higher severity alert, indicating potential brute-force activity.

Event Details (JSON Analysis)
Wazuh provides detailed JSON logs for each event, allowing deeper investigation.
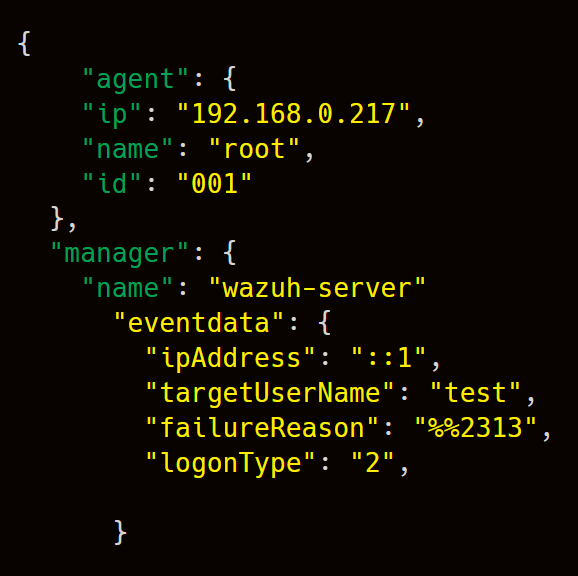
Key fields analyzed:
- targetUserName
- failureReason
- logonType
- ipAddress
Indicators of Activity
| Indicator | Value |
|---|---|
| Event ID | 4625 |
| Activity | Multiple failed logins |
| Detection | Correlated alert (Level 10) |
| Technique | T1110 (Brute Force) |
MITRE ATT&CK Mapping
T1110 – Brute Force
T1078 – Valid Accounts (potential follow-up)
Conclusion
This investigation demonstrates how multiple low-level authentication failures can be correlated into a high-confidence security alert.
It highlights the importance of:
- log collection and visibility
- event correlation in SIEM
- detection of abnormal authentication patterns
- investigation using raw event data
This reflects a real SOC workflow: logs → alerts → investigation.
Full Technical Project
View full investigation on GitHub: