Overview
This lab demonstrates DNS monitoring, traffic inspection and alert generation inside a home SOC environment.
The goal was to simulate suspicious network activity and analyze it using Pi-hole, Suricata IDS and Wireshark.
Lab Architecture
- ISP Router
- Raspberry Pi 4 (Pi-hole + Suricata IDS)
- Ubuntu VM (Traffic analysis)
- Windows 11 Host
- Wireshark (PCAP capture & inspection)
Detection Use Cases
- Suspicious DNS query analysis
- Blocked domain detection in Pi-hole
- Suricata alert triggered by suspicious traffic
- Manual PCAP inspection in Wireshark
Sample Evidence
This section presents real detection evidence collected from the lab environment:
- DNS query logs (Pi-hole)
- Packet capture validation (Wireshark)
- IDS alert generation (Suricata)
DNS Filtering Demonstration
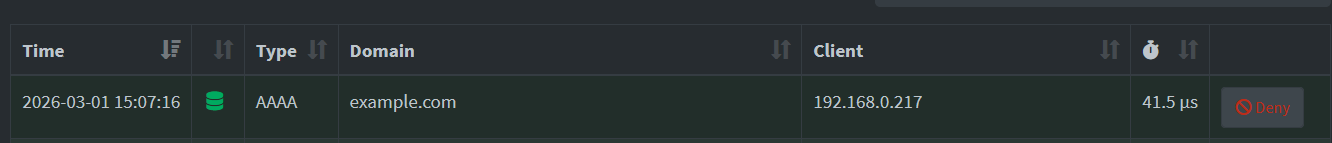
Caption:
DNS query for example.com observed from client 192.168.0.217 to Pi-hole (192.168.0.200).
The request was processed normally, demonstrating DNS visibility within the monitored network.
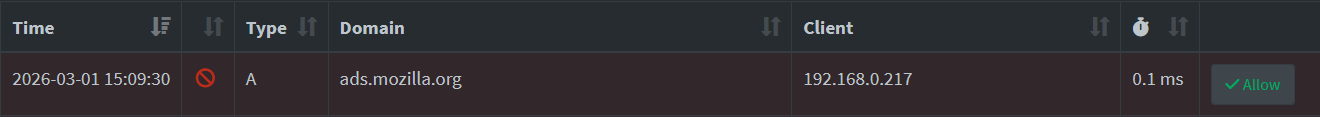
Caption:
DNS request for ads.mozilla.org was intercepted by Pi-hole and redirected at the DNS layer.
This demonstrates domain-level filtering and sinkhole behavior within the lab environment.
Packet-Level Inspection
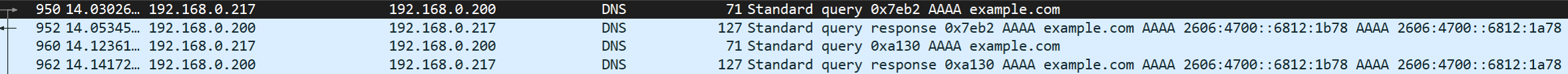
Caption:
Packet-level inspection of a DNS query and response for example.com.
The capture confirms correct DNS request/response flow and successful IPv6 resolution.
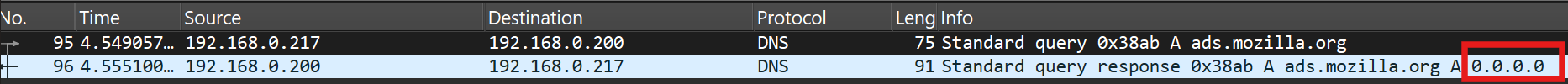
Caption:
DNS response returning 0.0.0.0 for ads.mozilla.org confirms that the block was enforced at the DNS layer.
Packet inspection validates filtering behavior beyond application-level logs.
IDS Alert Analysis
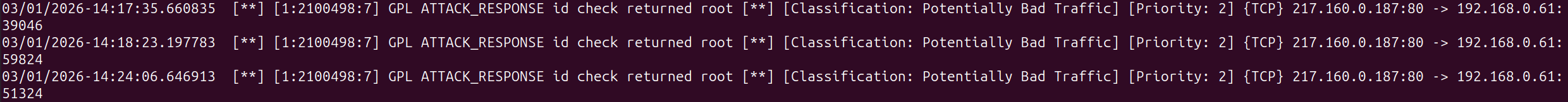
Caption:
Suricata generated a signature-based alert (SID: 2100498 – GPL_ATTACK_RESPONSE id check returned root).
Evidence from DNS logs, packet capture, and IDS alerts confirms multi-layer monitoring visibility and detection workflow validation.
Rule ID: 2100498
Classification: Potentially Bad Traffic
Priority: 2
The alert demonstrates that network activity was inspected and matched against detection rules from the Emerging Threats ruleset.This validates IDS monitoring capability within the lab environment.
Not all alerts represent malicious activity; rule context and traffic behavior must be evaluated before escalation.
The objective was not to simulate a full compromise but to validate monitoring visibility and detection workflow.
Suspicious DNS Query Analysis
During lab testing, a DNS query was intentionally generated from the test client (192.168.0.217) to simulate potentially suspicious outbound activity.
The query was observed in the Pi-hole DNS logs and further validated through packet-level inspection using Wireshark. The objective was to verify:
- DNS visibility
- Correct logging behavior
- Filtering enforcement
- Monitoring coverage across security layers
The test confirmed that:
- DNS queries were properly logged in Pi-hole
- Blocked domains were redirected to
0.0.0.0 - Legitimate domains resolved correctly
- Traffic could be validated at packet level
- IDS monitoring remained active during testing
This demonstrates that the monitoring stack provides visibility into outbound DNS behavior and allows multi-layer validation of security controls.
Technical Summary
Client IP: 192.168.0.217
DNS Server: 192.168.0.200 (Pi-hole)
Monitoring Tools: Wireshark, Suricata IDS
Detection Type: DNS filtering + signature-based alerting
Limitations
- IDS deployed in IDS mode (not inline IPS)
- No SSL/TLS decryption performed
- Home lab environment, not production traffic volume
Investigation Steps
- Generated DNS query to a test domain (example.com)
- Verified query in Pi-hole query log
- Captured traffic using Wireshark
- Inspected DNS request and response packets
- Confirmed correct logging and detection visibility
Lessons Learned
- DNS monitoring provides early insight into host intent before full connections are established.
- Packet-level validation is essential to confirm that security controls are functioning correctly.
- IDS alerts require contextual interpretation and cannot be treated as automatic indicators of compromise.
- Layered monitoring (DNS + PCAP + IDS) significantly improves analytical confidence.
- Detection visibility depends heavily on correct network placement and architecture design.