Overview
This project demonstrates a controlled phishing analysis workflow inside an isolated virtual environment.
The lab simulates safe investigation of suspicious URLs and phishing artifacts without exposing the host system.
Lab Architecture
- Host System: Windows 11
- Virtual Environment: VirtualBox (Ubuntu / Kali Linux)
- Network Mode: NAT / Host-Only isolation
- Traffic Monitoring: Wireshark (PCAP capture)
- Manual Analysis Tools: Browser DevTools, curl, dig, whois
+--------------------+
| Windows 11 Host |
|--------------------|
| VirtualBox |
+----------+---------+
|
| NAT / Host-Only
|
+----------v---------+
| Linux VM (Kali) |
|--------------------|
| Browser |
| Wireshark |
| curl / dig |
+----------+---------+
|
|
+----------v---------+
| Suspicious URL |
| Internet Traffic |
+--------------------+Investigation Workflow
- Suspicious URL initial inspection
- Domain and DNS reconnaissance (WHOIS / dig)
- Controlled detonation inside isolated VM
- Network traffic capture and PCAP analysis
- JavaScript and HTML source code review
- IOC extraction (IPs, domains, URLs, hashes)
- Structured incident documentation
Artifacts Collected
- PCAP file
- Extracted malicious domains
- Suspicious IP addresses
- HTTP request patterns
- Incident report template
Traffic Analysis Evidence
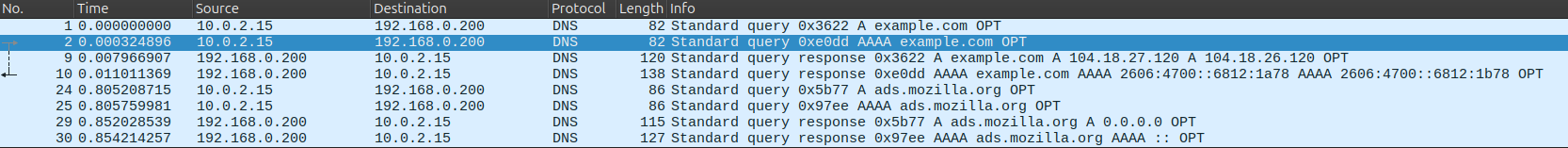
DNS resolution of suspicious domain inside isolated VM environment
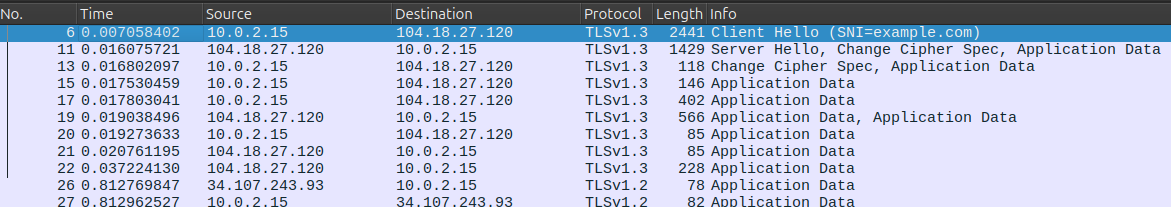
SNI field confirms the requested domain before encryption begins
Detection & Monitoring Considerations
During analysis the following detection opportunities were identified:
- DNS monitoring for newly registered or suspicious domains
- Detection of abnormal outbound HTTP requests
- Monitoring unusual User-Agent strings
- Detection of suspicious IP communication patterns
- Proxy log correlation with DNS queries
- SIEM correlation between DNS → HTTP → IP indicators
Mitigation Recommendations
- Block identified malicious domains and IPs at firewall level
- Add IOCs to DNS filtering solution (Pi-hole / enterprise DNS)
- Implement outbound traffic monitoring
- Apply browser security policies
- Conduct user awareness training
Key Skills Demonstrated
- Safe malware detonation procedures
- Network traffic analysis
- IOC identification and extraction
- Incident documentation
- Analytical workflow discipline
Lessons Learned
- Importance of VM isolation
- Value of packet-level inspection
- Pattern recognition in phishing infrastructure
- Importance of structured documentation