Project Summary
This project demonstrates a host-based detection lab where Sysmon telemetry from a Windows endpoint is collected and analyzed using Wazuh SIEM to detect suspicious PowerShell activity and map it to MITRE ATT&CK techniques.
Overview
This lab demonstrates Windows telemetry collection and security event analysis using Sysmon integrated with Wazuh SIEM.
The objective was to simulate suspicious host activity and validate detection visibility through Windows event logs and custom monitoring rules.
MITRE ATT&CK Techniques Observed
T1059.001 — PowerShell Execution
T1105 — Ingress Tool Transfer
These techniques were identified during simulated attack scenarios and validated through Sysmon telemetry and Wazuh SIEM detection.
Lab Architecture
Host System
- Windows 11 (Sysmon telemetry)
Monitoring Stack
- Ubuntu Server (Wazuh Manager)
- Wazuh Agent installed on Windows 11
Telemetry Source
- Microsoft Sysmon (Windows Event Log)
Detection Layer
- Wazuh rule engine
- Log correlation and alert generation
Architecture Diagram
Windows 11 Host
│
│ Sysmon Event Logs
│
Wazuh Agent
│
│ Log forwarding
│
Wazuh Manager (Ubuntu Server)
│
│ Rule matching
│
Alert generatedDetection Scenario
Simulated activity:
- Suspicious process execution
- Outbound network connection initiated by PowerShell
- PowerShell command execution
Investigation Workflow
- Sysmon installed on Windows host
- Wazuh agent configured to collect event logs
- Suspicious activity simulated
- Sysmon generated telemetry events
- Events forwarded to Wazuh manager
- Detection rule triggered
- Alert investigated in Wazuh dashboard
Threat Simulation
To validate detection capabilities, several suspicious PowerShell activities commonly observed in real-world attacks were simulated on the monitored host.
These scenarios demonstrate how endpoint telemetry collected by Sysmon can be analyzed and correlated in Wazuh SIEM.
Simulated Activities
PowerShell command execution
Encoded PowerShell command execution
Outbound HTTP request using PowerShell WebClient
Security Monitoring Dashboard
The Wazuh dashboard provides centralized visibility into security telemetry collected from monitored hosts.
Alerts generated from Sysmon events are correlated and visualized, enabling security analysts to quickly identify suspicious activity and investigate potential threats
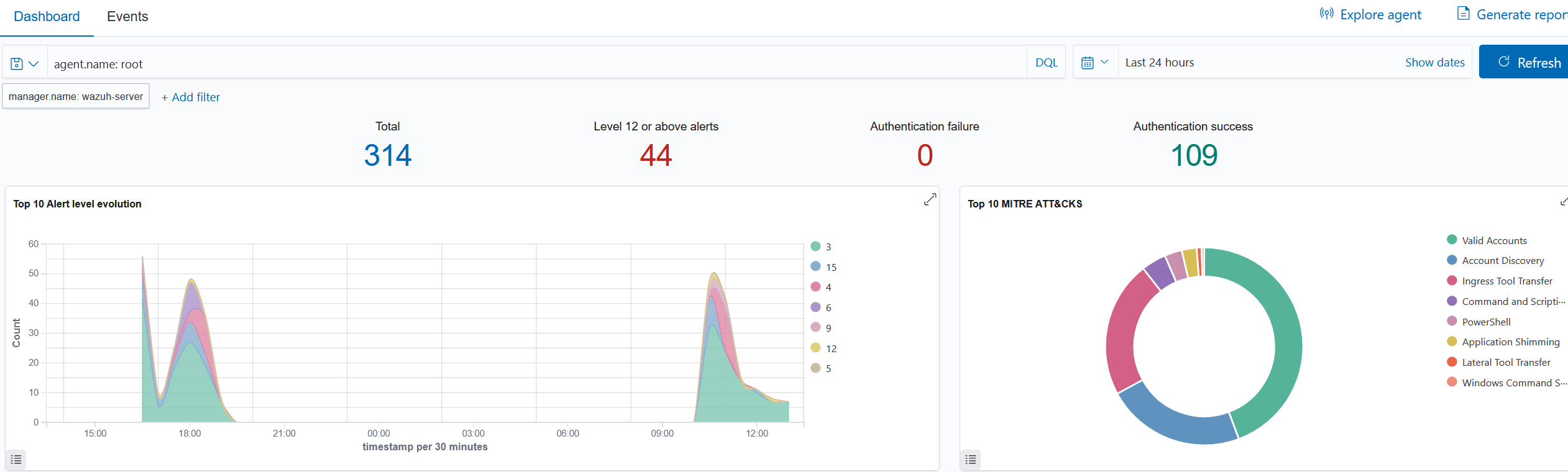
Wazuh SIEM dashboard displaying detected security events and threat activity based on Sysmon telemetry.
Evidence Collection
Scenario 1 — PowerShell Web Request
1. Attack Simulation
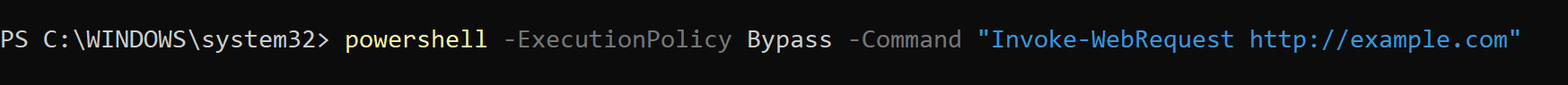
Caption:
Sysmon Event ID 1 capturing the execution of powershell.exe with the observed command-line arguments.
2. Sysmon Process Event
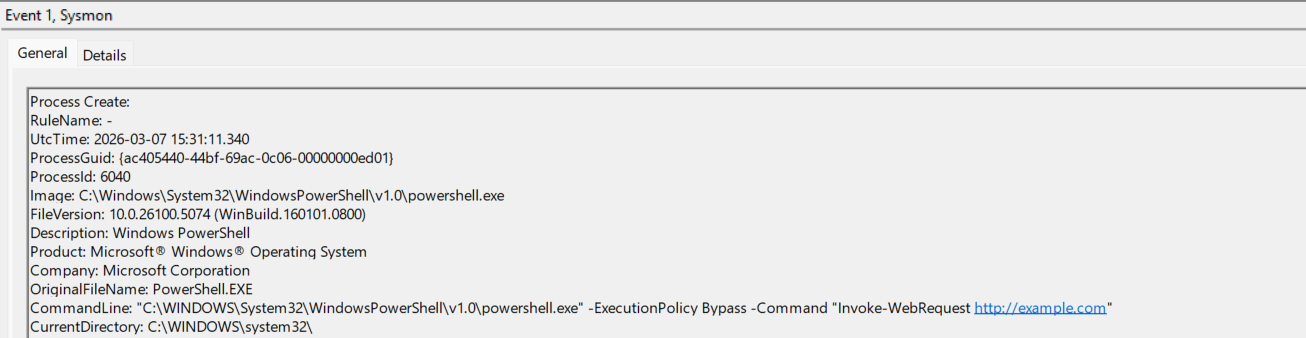
Caption:
Sysmon Event ID 1 capturing the execution of powershell.exe with the observed command-line arguments.
3. Sysmon Network Event (Event ID 3)
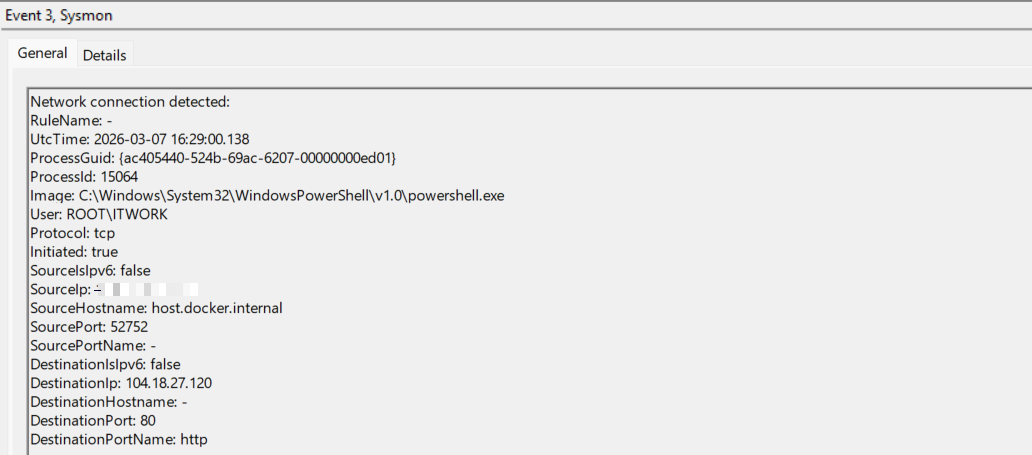
Caption:
Sysmon Event ID 3 showing an outbound HTTP network connection initiated by PowerShell.
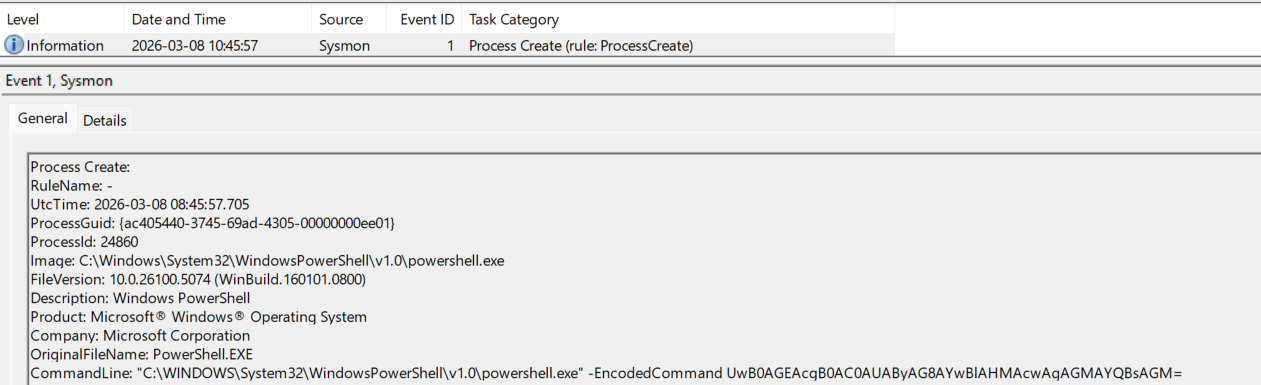
4. Wazuh Alert
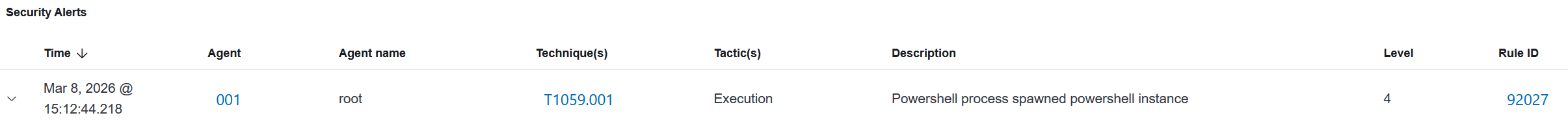
Caption:
Wazuh SIEM generated an alert mapped to MITRE ATT&CK technique T1059.001 (PowerShell Execution) based on Sysmon telemetry.
5.Wazuh Event Details
Detailed Wazuh event telemetry showing the PowerShell command line and process execution context collected from Sysmon logs.
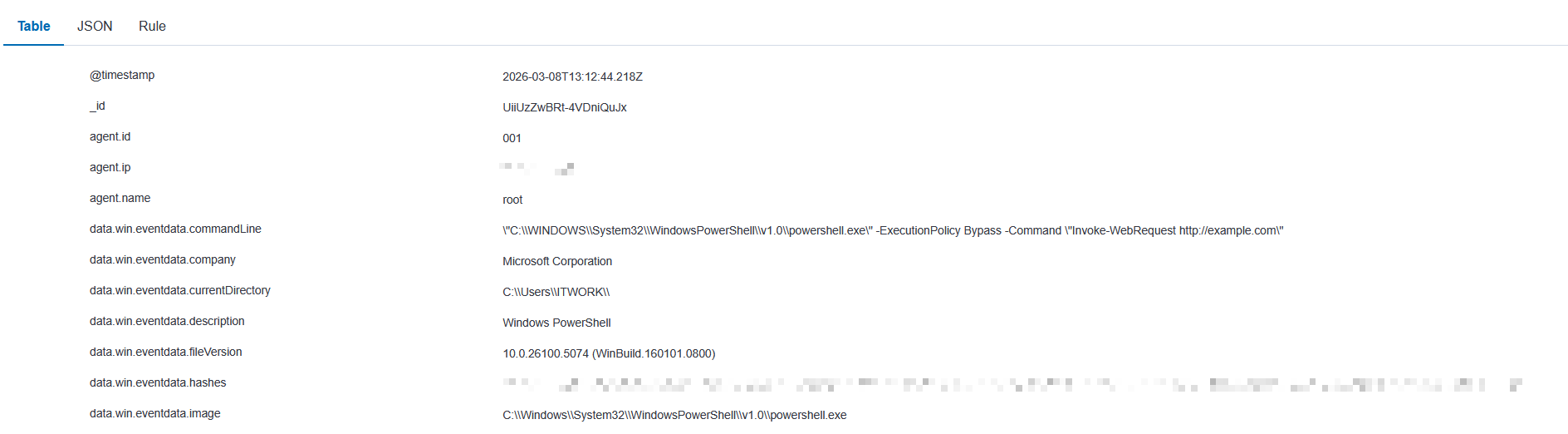
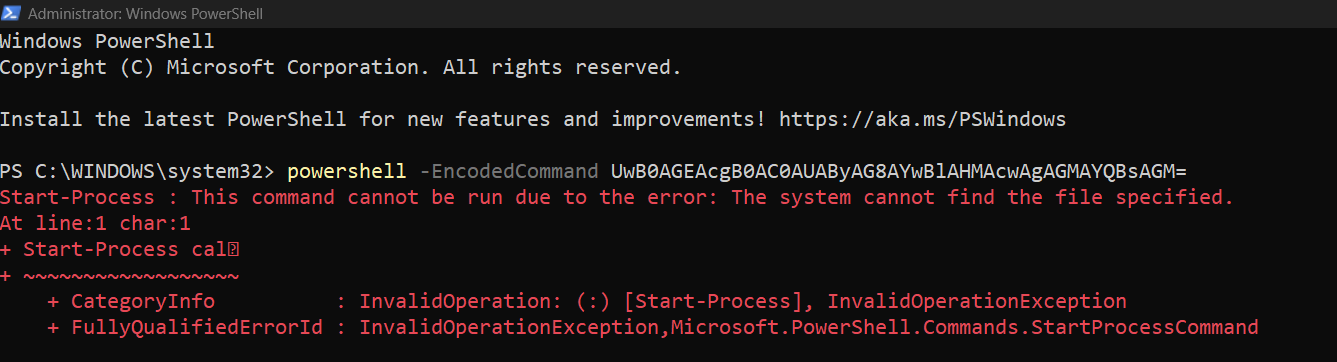
Scenario 2 — Encoded PowerShell Execution
1. Attack Simulation
Caption:
Encoded PowerShell command used to simulate obfuscated script execution commonly observed in malware.
2. Sysmon Process Event
Caption:
Sysmon Event ID 1 capturing the execution of PowerShell with the -EncodedCommand argument.
3. Sysmon Network Event
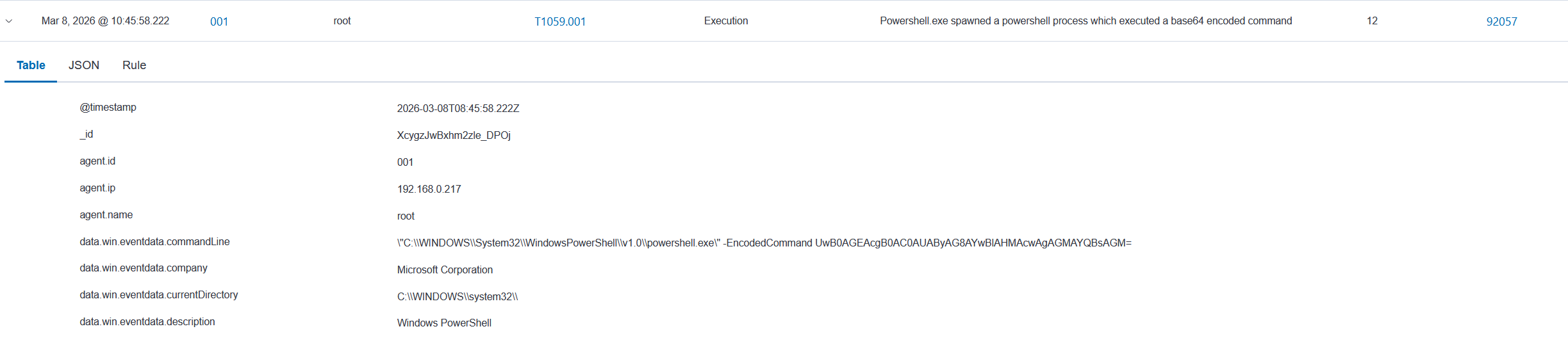
Caption:
Wazuh generated a detection mapped to MITRE ATT&CK technique T1059.001 (PowerShell) based on Sysmon telemetry.
Scenario 3 — PowerShell WebClient Network Activity
1 Attack Simulation
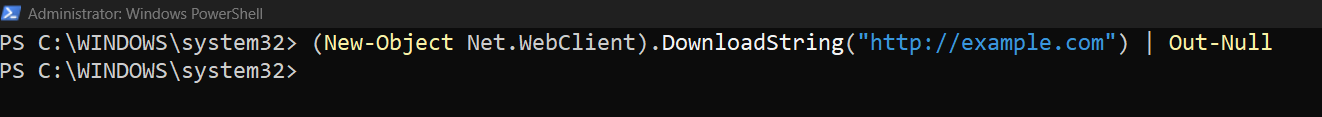
Caption:
PowerShell WebClient command used to simulate outbound HTTP activity from the monitored endpoint.
2. Sysmon Network Event (Event ID 3)
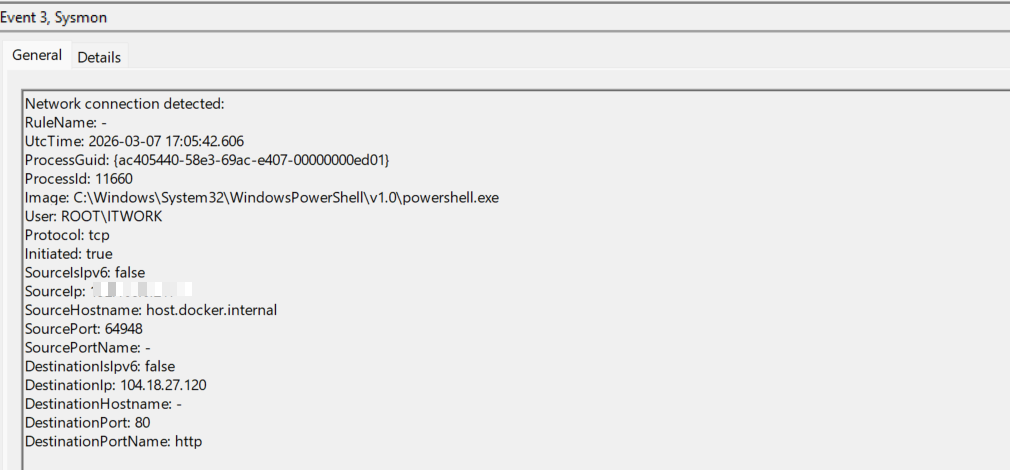
3. Sysmon Event ID 3 — Network Connection
Sysmon captured outbound HTTP activity initiated by PowerShell.
Wazuh successfully ingested the telemetry, demonstrating endpoint visibility even when a dedicated alert rule was not triggered.
Detection Opportunities
- Detection of suspicious PowerShell execution
- Monitoring unusual parent-child process relationships
- Detection of network connections from scripting engines
- Identification of abnormal command-line arguments
Detection Logic
Detection in this lab relies on Sysmon telemetry forwarded to Wazuh SIEM.
Wazuh rules analyze process creation events and command-line arguments to identify suspicious PowerShell activity.
Detection Indicators
- PowerShell process execution (powershell.exe)
- EncodedCommand parameter usage
- Suspicious PowerShell command-line arguments
- Outbound HTTP connections initiated by PowerShell
Telemetry Sources
- Sysmon Event ID 1 — Process Creation
- Sysmon Event ID 3 — Network Connection
- Windows Event Logs
- Wazuh rule correlation
Mitigation Recommendations
- Restrict PowerShell execution policies
- Implement EDR telemetry monitoring
- Alert on unusual parent-child process relationships
- Correlate endpoint and network telemetry
Key Skills Demonstrated
- Windows event log analysis
- Sysmon telemetry monitoring
- SIEM rule-based detection
- Threat investigation workflow
- MITRE ATT&CK mapping
Lessons Learned
- Host telemetry significantly improves detection visibility
- Sysmon provides granular process monitoring
- SIEM correlation enables centralized alert analysis
- Endpoint logs are critical for detecting post-exploitation activity
Conclusion
This lab demonstrates how Sysmon telemetry combined with Wazuh SIEM can be used to detect suspicious PowerShell activity, investigate alerts, and map detections to MITRE ATT&CK techniques.
The approach used in this lab reflects common SOC workflows where endpoint telemetry, SIEM correlation, and analyst investigation are combined to identify potentially malicious activity.